In an increasingly connected world, protecting your digital footprint has transitioned from a niche concern to a fundamental necessity for every internet user. Choosing NordVPN as your primary shield ensures that your sensitive data remains encrypted and shielded from the prying eyes of third-party trackers or malicious actors. As cyber threats become more sophisticated, the implementation of a high-tier virtual private network serves as the most effective baseline defense for maintaining anonymity while accessing global content without geographical restrictions or performance bottlenecks.Navigating the various installation pathways is the first step toward reclaiming your online freedom and ensuring total privacy across all your personal hardware. Whether you are looking to secure a professional workstation or a mobile device, the process is designed to be intuitive and rapid. By prioritizing a secure connection, you not only protect your financial information but also enjoy a faster, more open internet experience. The following comprehensive guide will detail the technical advantages of this industry-leading service and provide specific instructions for every major operating system platform.
In an increasingly connected world, protecting your digital footprint has transitioned from a niche concern to a fundamental necessity for every internet user. Choosing NordVPN as your primary shield ensures that your sensitive data remains encrypted and shielded from the prying eyes of third-party trackers or malicious actors. As cyber threats become more sophisticated, the implementation of a high-tier virtual private network serves as the most effective baseline defense for maintaining anonymity while accessing global content without geographical restrictions or performance bottlenecks.Navigating the various installation pathways is the first step toward reclaiming your online freedom and ensuring total privacy across all your personal hardware. Whether you are looking to secure a professional workstation or a mobile device, the process is designed to be intuitive and rapid. By prioritizing a secure connection, you not only protect your financial information but also enjoy a faster, more open internet experience. The following comprehensive guide will detail the technical advantages of this industry-leading service and provide specific instructions for every major operating system platform.
🛡️ Cybersecurity Excellence Summary
The service operates over 6,400 servers globally, utilizing the proprietary NordLynx protocol to deliver unmatched speeds. With a strict no-logs policy based in Panama and advanced features like Threat Protection Pro, it remains the gold standard for users seeking to combine extreme security with a seamless browsing and streaming experience.
Why this service remains the industry leader for privacy
The reputation of this provider is built upon a decade of consistent innovation and a relentless focus on user safety. One of the primary reasons experts recommend this platform is its jurisdiction in Panama, a country known for having no mandatory data retention laws. This allows the company to operate a verified no-logs policy, meaning that even if requested by authorities, there is simply no browsing history or connection data to provide. This legal foundation is a critical component for anyone who takes their personal data sovereignty seriously in the modern era.
Beyond the legal framework, the technical infrastructure is second to none. The network includes specialized servers for different tasks, such as Double VPN for extra encryption or Obfuscated servers for navigating environments with heavy internet restrictions. This versatility ensures that whether you are a casual browser or a high-level technical professional, the network adapts to your specific needs. The commitment to regular independent audits further solidifies the trust that millions of users place in the system every day to keep their communications private.
Furthermore, the integration of NordLynx technology has revolutionized what users expect from a encrypted connection. Based on the WireGuard® protocol, NordLynx offers the privacy of a tunnel without the traditional speed loss associated with legacy VPN technologies. This makes it the ideal choice for bandwidth-heavy activities such as high-definition streaming, competitive gaming, or transferring large files across the globe. By removing the friction between security and speed, the platform has successfully made high-level protection accessible to the general public without requiring any technical trade-offs.
Step by step guide to download nordvpn for Windows pc
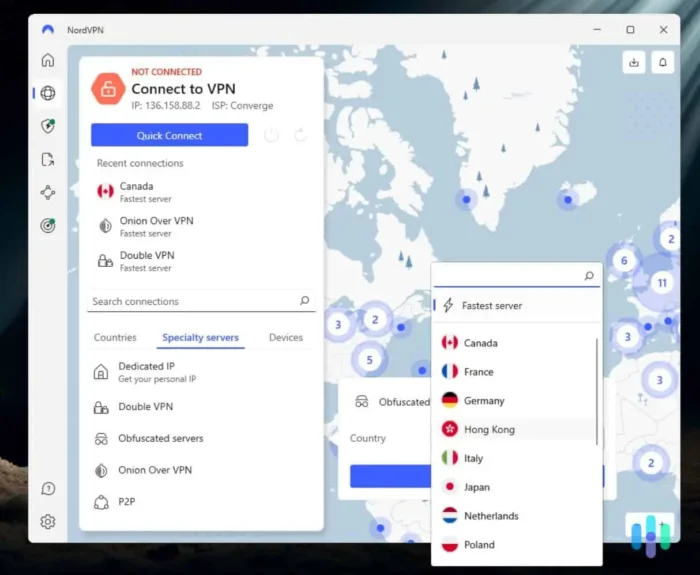
For those operating on desktop systems, the process to download nordvpn for Windows pc is engineered for maximum compatibility and ease of use. The application is optimized to run in the background with minimal system resource consumption, ensuring that your productivity is never hampered while your connection remains secure. Once the installation is complete, the “Quick Connect” feature identifies the optimal server based on your current location and server load, providing an instant shield for all your outgoing and incoming web traffic.
The Windows client includes several advanced features that are essential for power users. The Kill Switch is a vital safety mechanism that automatically blocks your internet access if the VPN connection drops unexpectedly, preventing any accidental data leaks. Additionally, the Split Tunneling feature allows you to choose which applications should use the encrypted tunnel and which should access the internet directly. This is particularly useful for accessing local network devices like printers while simultaneously keeping your web browser protected by the global server network.
To initiate the setup, users should always visit the official download center to ensure they are receiving the authentic, most recent version of the software. The installer handles the configuration of the network drivers automatically, making the entire setup process take less than three minutes. Once logged in, the intuitive map-based interface makes it easy to switch between countries with a single click, giving you the ability to virtually relocate your workstation to any of the 111 supported countries whenever necessary for research or media access.
✅ Installation Checklist for Desktop
- ✔Ensure your operating system is fully updated to avoid driver conflicts.
- ✔Download the official installer directly from the Nord Security portal.
- ✔Enable “Launch on Startup” to ensure you are protected from the moment you boot.
- ✔Run a leak test after your first connection to verify your new IP address.
Optimizing the experience for nordvpn download windows 11 systems

As Microsoft transitions users to its latest operating system, the nordvpn download windows 11 path has been specifically refined to take advantage of the new architecture. The software is fully compatible with the updated security features of the latest OS, including improved support for ARM-based devices. This ensures that whether you are using a traditional desktop or a modern ultrabook, the encryption engine operates at peak efficiency, utilizing the hardware-level security enhancements built into the latest processors.
For users seeking the Nordvpn download windows 11 64 bit version, the application automatically detects your system type during the installation process. This tailored approach ensures that the 64-bit binaries are deployed for maximum performance and stability. The interface has also been updated to match the aesthetic of the new Windows environment, featuring rounded corners and a clean design that integrates perfectly with the system tray. This visual consistency makes managing your privacy feel like a native part of your computing experience rather than an intrusive third-party add-on.
Advanced users on Windows 11 will also benefit from the improved Threat Protection Pro features. This isn’t just a simple ad-blocker; it acts as a comprehensive security layer that scans downloaded files for malware and blocks access to known malicious domains before they can load. By integrating these features directly into the network stack, the service provides an additional layer of safety that complements traditional antivirus software, creating a robust defense against the most prevalent modern web threats and tracking scripts used by advertisers.
Mobile security and nordvpn apk download latest version
The necessity for privacy extends far beyond the desk, as our mobile devices often contain the most sensitive personal information. Securing your smartphone with a Nordvpn apk download latest version is essential for anyone who frequently connects to public Wi-Fi networks in airports or cafes. Public hotspots are notorious for being insecure, often serving as prime targets for man-in-the-middle attacks where hackers intercept your data. A mobile connection ensures that your traffic is encrypted from the moment it leaves your phone, making your data unreadable to anyone else on the network.
While the application is readily available on the Google Play Store, some users prefer a direct download of the installation file for specific deployment needs. Obtaining the official nordvpn download android file directly ensures that you have the most up-to-date security patches even if you are in a region where store access is limited. The mobile app is designed to be extremely light on the battery, utilizing “auto-connect” features that activate the protection whenever an untrusted network is detected. This set-and-forget approach is perfect for busy individuals who need reliable security without constant manual intervention.
The mobile experience also includes the Meshnet feature, which allows you to create a secure, private tunnel between your own devices. This is incredibly useful for accessing files on your home computer while you are traveling or for sharing documents securely with colleagues. Meshnet bypasses the standard VPN server network and creates a direct encrypted link, providing a level of utility that goes far beyond simple web browsing. It effectively turns your collection of devices into a private cloud, protected by the same industry-leading encryption that secures the global server network.
| Feature | Basic Plan | Plus Plan | Complete Plan |
|---|---|---|---|
| High-Speed VPN | ✅ | ✅ | ✅ |
| Threat Protection Pro | ❌ | ✅ | ✅ |
| NordPass Manager | ❌ | ✅ | ✅ |
| 1 TB Cloud Storage | ❌ | ❌ | ✅ |
Advanced features: Beyond the standard encrypted tunnel
While many users choose this service for simple IP hiding, the platform offers a suite of advanced online security tools that address the full spectrum of modern digital risks. Threat Protection Pro is a standout feature that operates even when the VPN is not actively connected. it blocks web trackers that follow you from site to site, removes intrusive advertisements that clutter your experience, and prevents you from accidentally visiting phishing websites that might try to steal your credentials. This proactive approach ensures that your browsing environment remains clean and safe regardless of your connection status.
Another innovative tool is the Dark Web Monitor. This feature continuously scans underground forums and data leak repositories for your email address and personal information. If your data is found in a breach, the application sends you an immediate alert, allowing you to change your passwords before attackers can exploit the information. In a time where major corporate data breaches occur weekly, having an automated system watching your back is a significant value-add that provides real peace of mind for both individuals and small business owners alike.
For those who require the highest level of anonymity, the “Onion Over VPN” servers offer a unique solution. This feature combines the benefits of a VPN tunnel with the Tor (The Onion Router) network, routing your data through multiple layers of encryption and several volunteer-run nodes. This makes it virtually impossible for anyone to trace your activity back to your physical location. While this method may lead to slightly lower speeds due to the multiple hops, it is the ultimate tool for journalists, activists, or anyone operating in high-risk digital environments where absolute privacy is the only acceptable standard.
💡 Expert Optimization Tip
If you are experiencing any connectivity issues or slower speeds, try switching your protocol from “Auto” to “NordLynx” in the application settings. This often provides an immediate performance boost by utilizing the most modern encryption technology available. Additionally, choosing a server in a neighboring country rather than one across the globe will always result in lower latency for gaming and video calls.
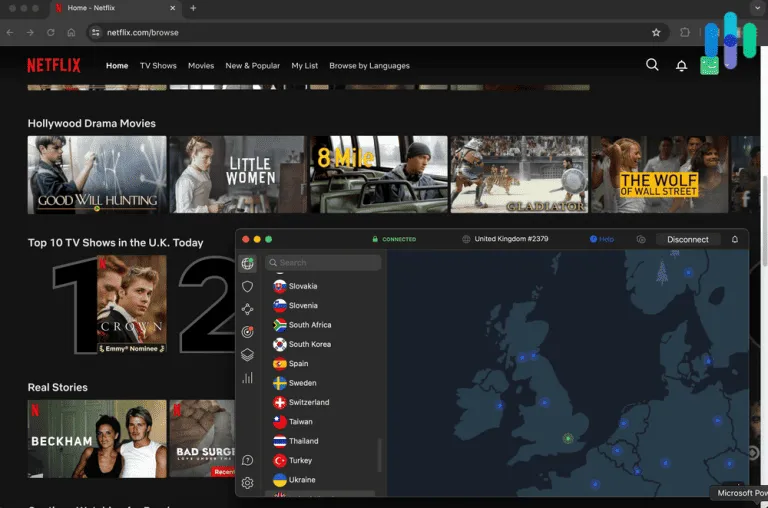
The importance of server locations and global access
The vast network of over 6,300 servers across 111 countries is a major differentiator for this provider. This scale ensures that no matter where you are, you can always find a fast, local server to minimize latency. For international travelers, this is a game-changer. You can virtually return to your home country to access local news, banking services, or streaming libraries that might be blocked while you are abroad. This ability to bypass “geo-blocking” ensures that your digital subscriptions remain useful regardless of your physical location, making it an essential tool for the modern digital nomad.
Furthermore, the provider offers dedicated IP addresses for those who need a consistent online identity. Traditional VPNs assign you a shared IP address, which can sometimes lead to “CAPTCHA” fatigue as websites see multiple users from the same origin. A dedicated IP is yours alone, providing the security of a VPN with the stability of a static address. This is particularly useful for accessing business servers or remote work environments where IP-based whitelisting is required for security. It offers the perfect balance of privacy and professional utility, ensuring you can work from anywhere without technical friction.
Reliability is also maintained through constant hardware upgrades. The company is currently transitioning its entire network to 10Gbps servers, preparing for the future of ultra-high-bandwidth internet. This investment in physical infrastructure ensures that as global internet speeds increase, your protection will not become a bottleneck. By staying ahead of the curve, the provider guarantees that their users will continue to enjoy a premium experience for years to come, reinforcing their position as the preferred choice for high-performance cybersecurity solutions across the globe.
Managing your subscription and multi-device support
One of the most user-friendly aspects of the service is the ability to protect up to ten devices with a single account. In the modern household, where it is common to have multiple laptops, smartphones, tablets, and even smart TVs, this multi-device support is a massive cost-saver. You don’t have to choose which device to protect; you can secure your entire digital ecosystem simultaneously. The application is available for almost every platform, including macOS, Linux, and even specialized versions for routers, ensuring that even devices that don’t support VPN apps natively—like gaming consoles—can benefit from the encrypted network.
Managing these connections is simplified through a centralized account dashboard. From here, you can see your active subscriptions, update your billing information, and even access the NordPass password manager or NordLocker encrypted cloud storage if they are included in your plan. This integration of services under one umbrella makes it easy to stay organized and ensures that all your security tools are working in harmony. If you are planning a journey and need to coordinate your logistics, you might also find this travel planning guide useful for organizing your itinerary with the same level of precision and security.
The 30-day money-back guarantee is another significant feature that allows new users to test the full range of services completely risk-free. If for any reason you are not satisfied with the speed, features, or server selection, you can request a full refund within the first month. This transparent approach demonstrates the company’s confidence in their product and allows consumers to verify the claims of industry-leading performance for themselves. It removes the barrier to entry for those who are still undecided, making it easier than ever to take the first step toward a more secure digital life.
“The digital landscape of 2026 demands a proactive stance on privacy. Waiting for a breach to happen is no longer an option; we must build our defenses today with the best tools available. High-level encryption is the new basic requirement for digital citizenship.”
Customer support and the 24/7 reliability factor
No technical service is complete without a robust support system, and this provider excels by offering 24/7 live assistance. Whether you have a complex question about configuring your router or a simple inquiry about your billing cycle, professional help is always just a few clicks away via the live chat interface. The support team is highly trained and capable of resolving most technical issues in real-time, ensuring that you are never left unprotected due to a configuration error. This commitment to customer care is a hallmark of a mature, global service provider that values the time and safety of its diverse user base.
In addition to the live chat, the extensive help center provides a wealth of self-service resources. Detailed tutorials, video guides, and troubleshooting articles cover every conceivable scenario, from setting up the service on a Firestick to understanding the nuances of the “Double VPN” feature. This educational approach empowers users to take control of their own security and learn more about how the digital world works. By providing the tools and the knowledge, the company helps create a more informed and resilient online community, which is essential for the long-term health of the global internet ecosystem.
Reliability also extends to the uptime of the server network. The company utilizes advanced monitoring systems to detect and resolve server issues before they affect the user experience. If a particular server is undergoing maintenance or experiencing a high load, the “Quick Connect” algorithm will automatically steer you toward a more stable alternative. This high level of operational excellence ensures that your protection is consistent and dependable, allowing you to focus on your work or leisure with the confidence that your digital shield is always active and performing at its best.
In conclusion, the decision to invest in premium protection is one of the smartest moves you can make in the digital age. By choosing the right tools and following the proper installation steps, you are taking a definitive stand for your personal privacy and safety. Whether you are using a desktop at home or a mobile device on the go, the world’s most trusted network is there to ensure your journey is fast, secure, and entirely your own. Don’t wait for your data to be compromised—start your journey toward digital mastery today and enjoy the internet the way it was meant to be: open, fast, and completely private.
Ready to Reclaim Your Privacy?
Join millions of users who trust the world’s leading VPN provider to keep their data safe. With unmatched speeds, a verified no-logs policy, and a 30-day money-back guarantee, there has never been a better time to secure your digital life.
Risk-Free 30-Day Money-Back Guarantee Included